Shadow IT Exposes 40% of Your Infrastructure to Ransomware and Nation-State Attacks
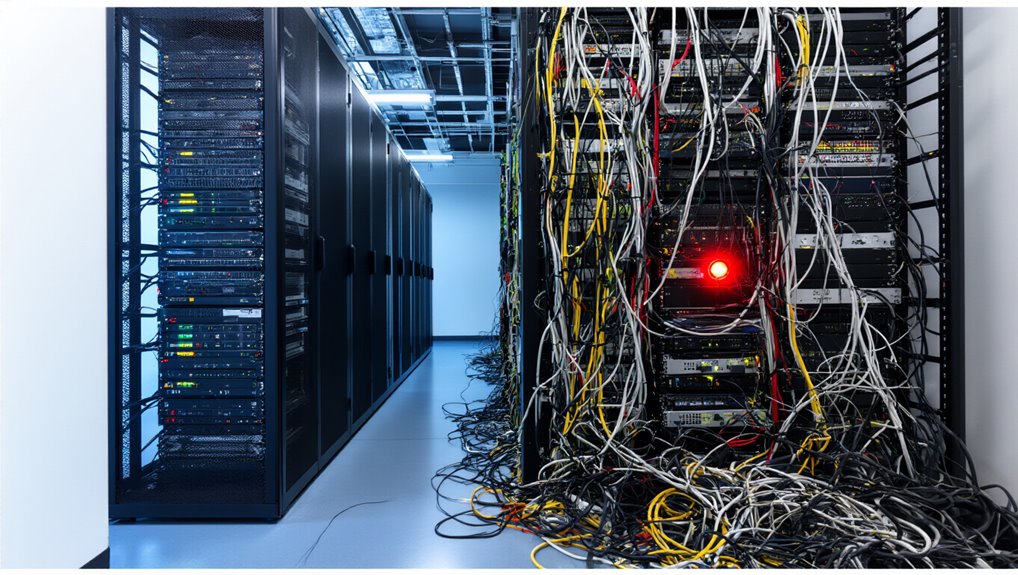
How much of your organization’s infrastructure operates beyond your security team’s visibility? Research shows 61% of security leaders cannot identify and remediate cloud exposures, while developers routinely spin up unsanctioned cloud resources outside governance frameworks. This shadow IT infrastructure creates dangerous blind spots that attackers actively exploit.
Organizations face alarming consequences: 75% experienced cyberattacks in the past 24 months, with shadow IT increasing breach costs by $670,000 per incident. Only 9% validate cloud exposures daily, leaving systems vulnerable to ransomware deployment and nation-state infiltration through unmonitored entry points that traditional detection methods fail to identify. Implementing robust encryption and unified API management can reduce these risks and improve visibility across cloud services.
Why CMDBs and Vulnerability Scanners Miss Ephemeral Cloud VMs and IoT Devices?
Shadow IT flourishes partly because traditional asset management tools weren’t built for today’s infrastructure. CMDBs evolved for static systems and fail to track containers or auto-scaling instances that appear overnight. Vulnerability scanners running weekly can’t keep pace when developers deploy ten containers in one afternoon, leaving CMDBs 30% inaccurate.
Traditional asset management tools built for static systems cannot track the ephemeral infrastructure modern developers deploy at speed.
Three critical gaps emerge:
- Cloud VMs evade detection between scan cycles, with forgotten resources missed entirely by network sensors
- IoT devices act as black boxes, not responding to pings or allowing agent installation
- OT environments prohibit active scanning due to safety risks, forcing slower passive monitoring
Integrated systems that connect inventory, BI, and security tooling can shrink these blind spots by enabling real-time discovery and correlation with business intelligence.
What Happens When Undocumented Assets Get Breached: Incident Response Gaps That Cost Millions?
Undocumented assets transform security incidents into catastrophic business failures because response teams cannot defend what they don’t know exists.
When breaches occur on unknown systems, organizations face 279 days average detection time, costing $4.88 million per incident. Your security team cannot investigate logs, patch vulnerabilities, or contain threats on devices absent from asset inventories.
Credential-based breaches affecting undocumented resources require 328 days to resolve—51 additional days of exposure.
Financial sector organizations suffer $6.08 million losses when unknown assets compromise networks.
Without asset documentation, you cannot determine breach scope, notify affected parties, or implement corrective controls, multiplying regulatory penalties and customer trust damage exponentially.
Strong data integrity practices and regular system audits reduce the likelihood of unknown assets and help prevent these outcomes.
Finding Shadow IT: Automated Discovery Tools That Map APIs, Containers, and Rogue SaaS
Modern organizations lose visibility of 40-60% of their technology stack within twelve months of deployment, creating blind spots where unauthorized APIs, containerized workloads, and rogue SaaS applications operate beyond security controls.
Automated discovery tools now solve this problem through multi-vector detection:
- Identity-first discovery ingests SaaS audit logs and correlates users with OAuth apps, detecting shadow IT based on actual usage patterns
- AI-powered engines analyze financial transactions and expense reports to identify both known and unknown applications across 125,000+ application databases
- Token inspection reveals access permissions down to individual Slack bots while usage metering distinguishes casual trials from full adoption
These tools integrate with SSO systems, SIEM platforms, and finance software for holistic visibility. Organizations leveraging APIs are 24% more likely to achieve profitability, making proactive discovery and governance an essential part of security and business strategy.
Cloud Sprawl and Kubernetes Blind Spots Your Security Team Can’t Inventory Manually
While automated discovery tools reveal SaaS applications and API connections, cloud infrastructure presents a different challenge altogether. Organizations running Kubernetes across multiple providers like EKS, AKS, and GKE face expanded attack surfaces with orphaned workloads and open ports your team can’t manually track.
The numbers tell the story: 43% of cloud environments remain vulnerable to known CVEs affecting over 6,500 clusters. Manual inventory becomes impossible when managing hundreds of clusters, leading to configuration drift and version skew. Without automated visibility, you’re left with ungoverned shadow IT clusters, inconsistent IAM policies, and exploitable gaps that attackers leverage for lateral movement. Organizations also struggle with the complexity of integration environments that create maintenance burdens and increase the risk of oversight.
Building a Living Asset Inventory That Updates Faster Than Developers Spin Up Resources
In environments where infrastructure-as-code pipelines can provision hundreds of resources in minutes, traditional asset inventory methods fail before they finish their first scan. You need automated discovery running continuously across AWS, Azure, GCP, and on-premises systems. Deploy agent-based tools for managed devices and agentless scanning for network infrastructure.
Three requirements for keeping pace:
- Real-time API integration with cloud providers capturing new resources instantly
- Passive discovery tools detecting configuration changes as they happen
- Centralized normalization creating one unique record per asset across all sources
Route live observations into a single dashboard, eliminating manual updates and maintaining one authoritative inventory.
Map Shadow IT to SOC 2 and Cyber Insurance Requirements Without Manual Audits
Asset discovery reveals infrastructure you manage—shadow IT exposes the systems your organization uses without permission. This distinction matters for SOC 2 audits and cyber insurance, where undocumented apps create compliance gaps.
Cloud Access Security Brokers (CASB) and Secure Web Gateways (SWG) provide traffic visibility to detect unauthorized tools automatically. Data Loss Prevention (DLP) flags exfiltration attempts through shadow apps. OAuth management controls which services access your data.
Deploy browser extension whitelisting and Mobile Device Management (MDM) to enforce endpoint controls. Insurance providers require proof of controls over all data-handling applications—shadow AI bypasses vendor risk assessments, triggering coverage denials and premium increases.